Results for "attack clones"
Attack clones refer to a type of technology or strategy used in various fields, including gaming and robotics, where duplicate entities are created to perform tasks or engage in combat. These clones can enhance efficiency and effectiveness in operations.

4.6
80 sold
-47%$40.70$76.79
![Xerjoff Erba Pura Eau De Parfum Unisex [ DECANT 5 ML / 0.17 OZ ] Xerjoff Erba Pura Eau De Parfum Unisex [ DECANT 5 ML / 0.17 OZ ]](https://p16-oec-general-useast5.ttcdn-us.com/tos-useast5-i-omjb5zjo8w-tx/f49cb5b081b447ac8f206f84ce56653b~tplv-fhlh96nyum-crop-webp:300:300.webp?dr=12190&t=555f072d&ps=933b5bde&shp=8dbd94bf&shcp=a6e80448&idc=useast5&from=2378011839)


BASED

4.6
36.2K sold
-50%$15.00$30.00


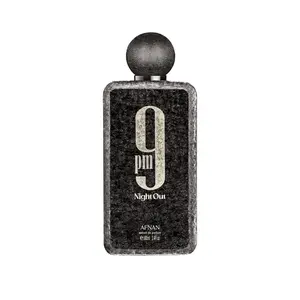
Afnan Perfumes USA

4.8
4.3K sold
-25%$44.99$60.00


4.7
21.8K sold
-41%$46.90$79.95



3.8
47.8K sold
-50%$14.98$30.00
Related Searches
Related Categories
Introduction
In the realm of gaming and technology, attack clones play a pivotal role in enhancing strategic gameplay and operational efficiency. Often utilized in multiplayer games, these clones allow players to deploy multiple avatars or units simultaneously, creating a tactical advantage over opponents. The concept of attack clones is not only limited to gaming but extends to robotics and artificial intelligence, where duplicates can be programmed to execute complex tasks.
When considering the implementation of attack clones, it's essential to understand their benefits:
Trusted by thousands of gamers and tech enthusiasts, the use of attack clones has proven to enhance the overall experience and effectiveness in both virtual and physical environments. Regular updates and advancements in technology continue to improve their capabilities, making them a valuable asset in various applications. Stay informed about the latest trends and strategies related to attack clones to maximize their potential in your endeavors.
When considering the implementation of attack clones, it's essential to understand their benefits:
- Increased Efficiency: Attack clones can perform tasks faster than a single entity, allowing for quicker completion of objectives.
- Enhanced Strategy: Players can create diversions and flanking maneuvers, making it harder for opponents to predict actions.
- Resource Management: Effective use of clones can lead to better resource allocation in games and real-world applications.
Trusted by thousands of gamers and tech enthusiasts, the use of attack clones has proven to enhance the overall experience and effectiveness in both virtual and physical environments. Regular updates and advancements in technology continue to improve their capabilities, making them a valuable asset in various applications. Stay informed about the latest trends and strategies related to attack clones to maximize their potential in your endeavors.






![Star Wars: Episode II: Attack of the Clones [4K ULTRA HD BLU-RAY MOVIE] With Blu-Ray, 4K Mastering, Collector's Ed, , Dolby, Dubbed, Subtitled, Ac-3/Dolby Digital Star Wars: Episode II: Attack of the Clones [4K ULTRA HD BLU-RAY MOVIE] With Blu-Ray, 4K Mastering, Collector's Ed, , Dolby, Dubbed, Subtitled, Ac-3/Dolby Digital](https://p16-oec-general-useast8.ttcdn-us.com/tos-useast8-i-rt0ujvrtvp-tx2/32a72c7b45af47d0ab6aab8f7c203d3d~tplv-fhlh96nyum-crop-webp:247:300.webp?dr=12190&t=555f072d&ps=933b5bde&shp=8dbd94bf&shcp=a6e80448&idc=useast5&from=2378011839)


















